Understanding the identity of Sebastian Dante Alexander
It has come to my attention that Sebastian could be no other person than Michael Errington himself
How it all started?
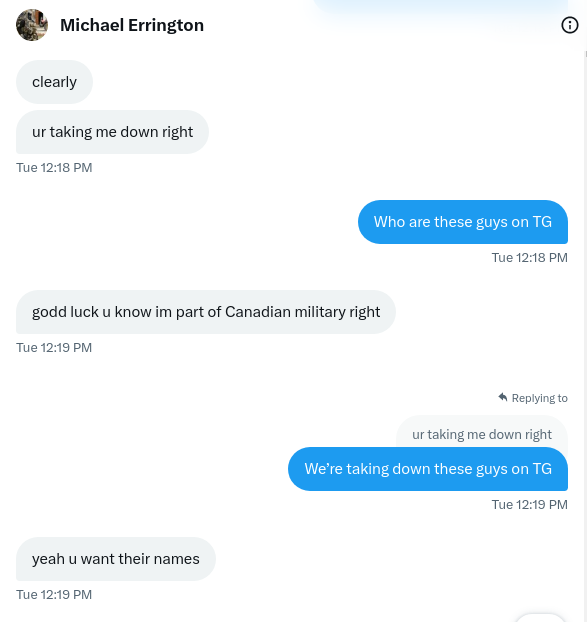
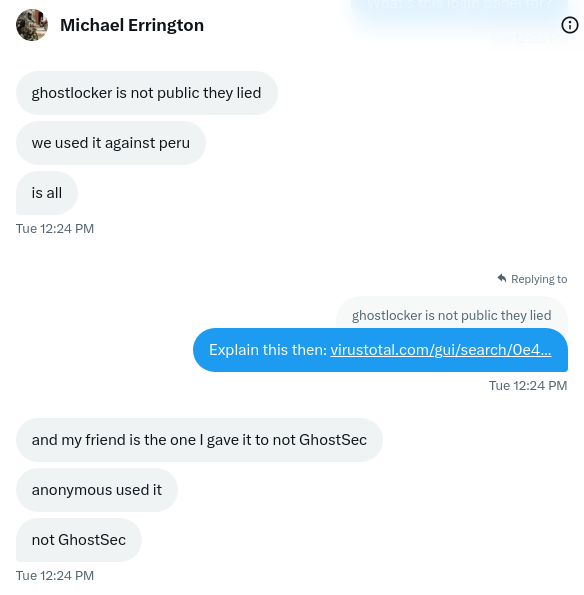
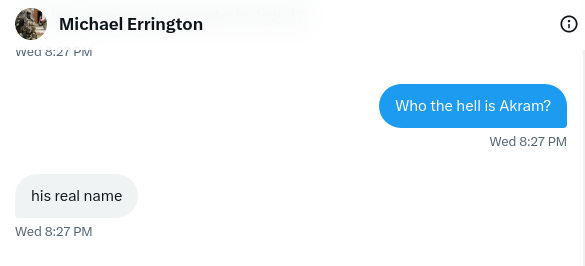
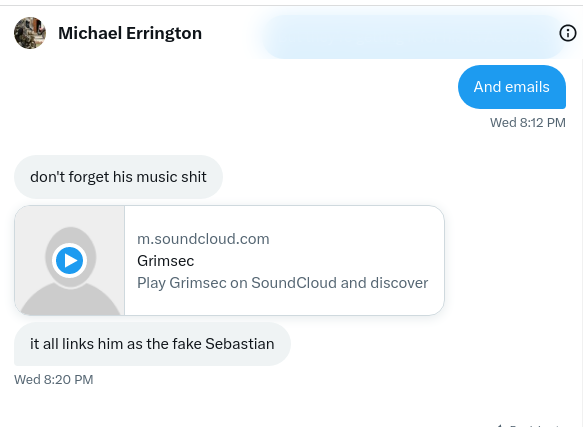
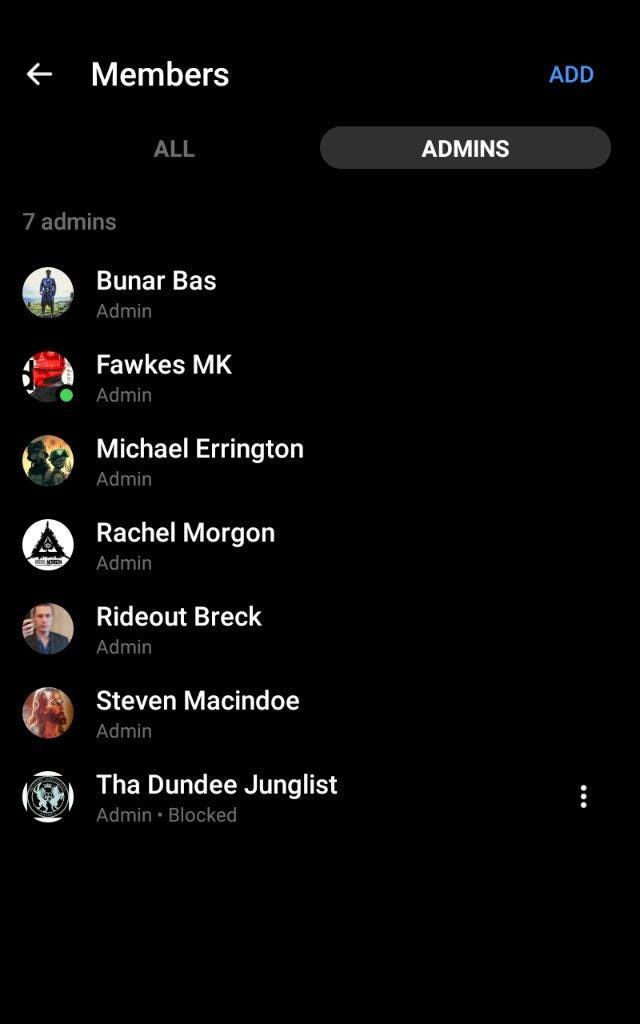
It all happened earlier the day before yesterday that during the time when I was trying to find a sample of the GhostLocker Malware to perform analysis and release a report on my Medium and my Research Gate that I managed to meet up with Michael Errington, who told me he was disabled and that he was the real Sebastian, using Sebastian’s real name over his emails and even creating tools for GhostSec which includes the GhostLocker that GhostSec currently has, saying that the GhostLocker wasn’t used in over ten years or more. He said that the fake GhostSec Channel in Telegram run and go by the identity of GrimSec and not GhostSec, and that the owners real name of the fake GhostSec in Telegram is actually Akram, whose a 24-Year Old Lebanese. He further even went on to claim that he’s part of the Canadian Military as well.
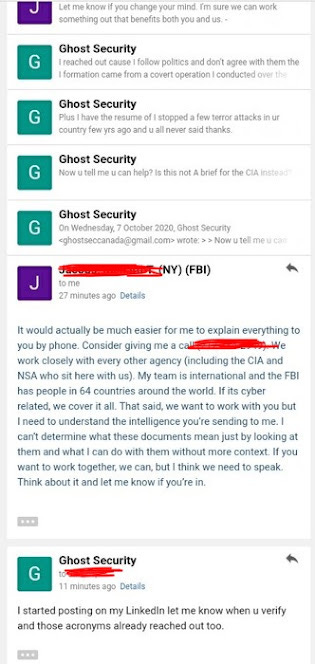
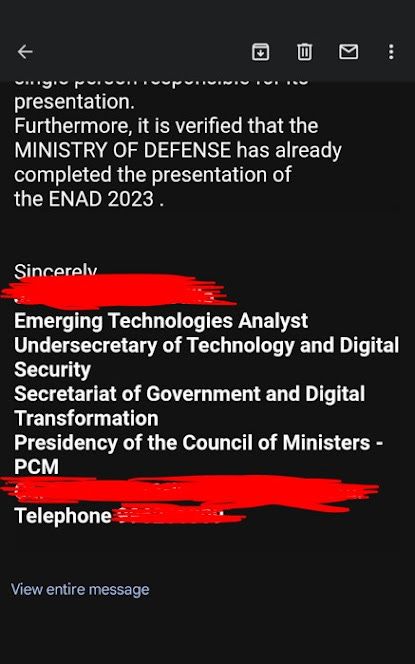
Once again, he told me that the Sebastian in Telegram is fake because the real GhostSec wouldn’t use Telegram because they have tested multiple vulnerabilities on it, all in all, he convinced me that he works with the Federal Authorities by showing me emails he has had with the FBI and The Council of the President in Peru.
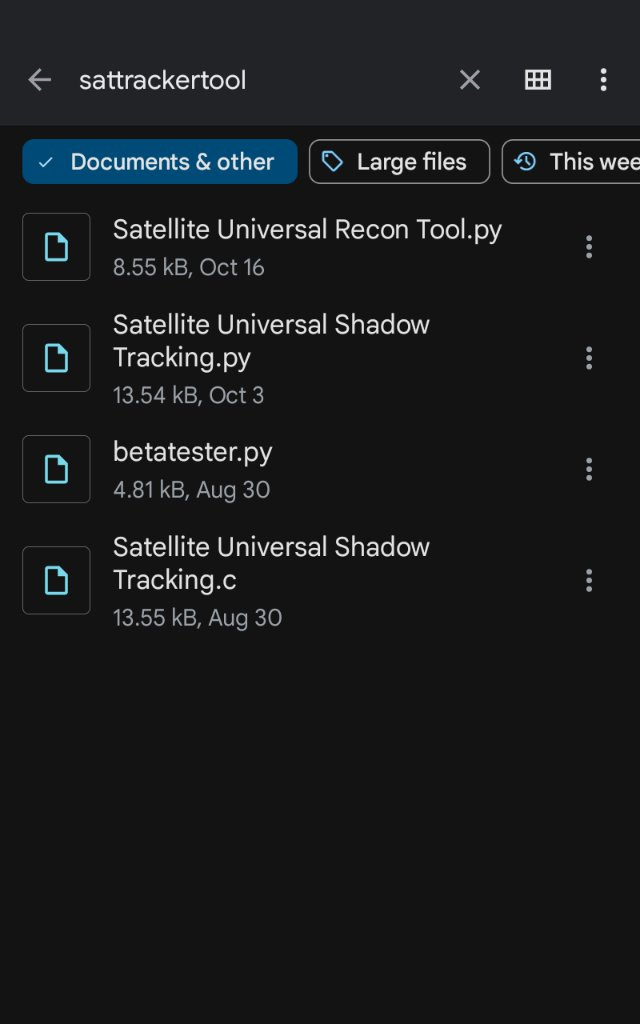
He showed me tools that he created for the Canadian Armed Forces and people on his friendlist on Social Media who identify themselves as the CIA, which made me fall for his manipulative lie that he could be saying the truth.
# Comprehensive Mapping System for Universal Satellite Shadow Analysis # Introduction: This comprehensive mapping system utilizes satellite data to identify shadowed areas on the globe, providing detailed information about shadow paths, densities, and estimated shadow window times. The system includes a mapping overlay system, a tracking component for satellites, and a robust code structure to enhance readability and maintainability.
# Mapping Overlay System: The mapping overlay system incorporates satellite data with geographic information to create visual representations of shadowed areas worldwide. This system uses a mapping library, such as Google Maps API, to display the shadow paths and densities effectively. # Satellite Tracking Component: The satellite tracking component enables the system to track the position and time of each satellite, allowing for accurate analysis of shadowed areas. This component collects real-time data from satellite tracking sources, such as NORAD or dedicated satellite tracking systems.
# Data Compilation and Analysis: To determine the exact coordinates and times that create a window of shadow on the satellite and radar data, the system combines the satellite tracking data with existing satellite images and radar information. This data compilation process ensures that all relevant information is considered.
# Universal Shadow Spot Identification: Using the compiled data, the system analyzes the shadow paths and densities to identify areas that are persistently shadowed due to the elapsed time the satellites pass over. The result is a comprehensive mapping of universal shadow spots, providing valuable insights and information.
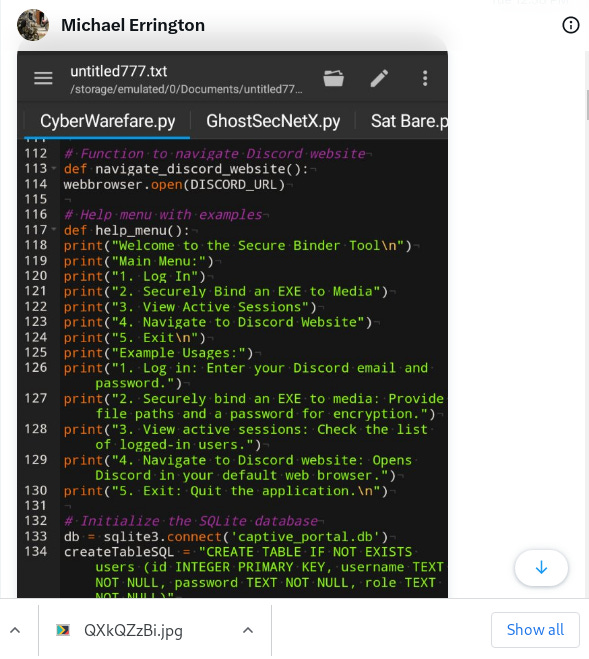
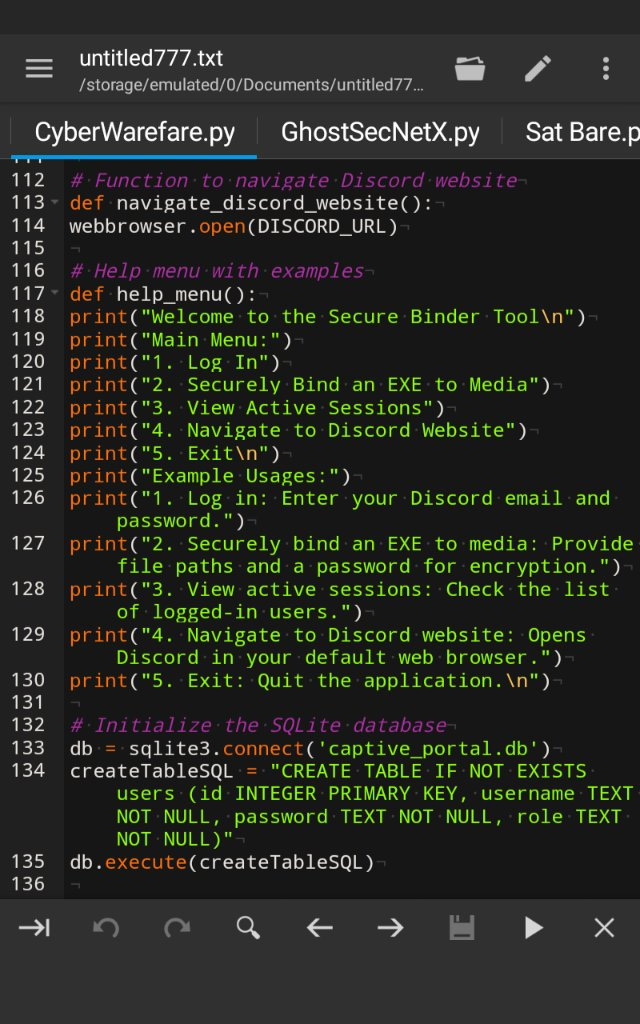
He even further proves himself as a hacker by sending in his Captive Portal that he was making to use fernet encryption method with AES Algorithm to encrypt traffic (What are the coincidences that the same encryption method (Fernet) is used in both the GhostLocker Ransomware and the Captive Portal?)
#!/usr/bin/env python import os import signal import threading import netfilterqueue from scapy.all import * from flask import Flask, render_template import iptc from cryptography.fernet import Fernet import hashlib app = Flask(__name__) encryption_key = Fernet.generate_key() fernet = Fernet(encryption_key) def log_event(event_type, message): with open("audit_log.txt", "a") as log_file: log_file.write(f"{event_type}: {message}\n") def redirect_traffic(packet): try: log_event("REQUEST", packet.load) if apply_microsegmentation(packet): packet.accept() else: packet.drop() except Exception as e: log_event("ERROR", str(e)) def apply_microsegmentation(packet): if packet.haslayer(IP): src_ip = packet[IP].src dst_ip = packet[IP].dst if (src_ip == "trusted_subnet" and dst_ip == "trusted_subnet") or \ (src_ip == "dmz_subnet" and dst_ip == "dmz_subnet"): return True else: return False return False def start_captive_portal():
@app
.route("/") def captive_portal(): try: user_agent = request.headers.get("User-Agent") log_event("USER_AGENT", user_agent) return render_template("captive_portal.html") except Exception as e: log_event("ERROR", str(e)) return "An error occurred."
http://app.run
(host="0.0.0.0", port=80, ssl_context=("path/to/cert.pem", "path/to/key.pem")) def dns_spoofing(packet): try: log_event("DNS_REQUEST", packet[DNS].qd.qname) send(packet, verbose=0) except Exception as e: log_event("ERROR", str(e)) def simulate_wireless_printer(): while True: print("Simulated Printer received:", packet.load) def setup_microsegmentation(): try: os.system('iptables -A FORWARD -s trusted_subnet -d trusted_subnet -j ACCEPT') os.system('iptables -A FORWARD -s dmz_subnet -d dmz_subnet -j ACCEPT') os.system('iptables -A FORWARD -j DROP') except Exception as e: log_event("ERROR", str(e) def setup_logging(): pass def hash_password(password): sha256 = hashlib.sha256() sha256.update(password.encode()) return sha256.hexdigest() def authenticate(username, password): stored_password = get_stored_password(username) hashed_password = hash_password(password) return stored_password == hashed_password def get_stored_password(username): stored_passwords = { 'user1': 'hashed_password1', 'user2': 'hashed_password2', } return stored_passwords.get(username, '') def main(): try: if len(sys.argv) > 1: start_captive_portal_flag = False log_flag = False microsegment_flag = False dns_spoofing_flag = False printer_sim_flag = False for arg in sys.argv[1:]: if arg in ['-s', '--start']: start_captive_portal_flag = True if arg in ['-l', '--log']: log_flag = True if arg in ['-m', '--microsegment']: microsegment_flag = True if arg in ['-d', '--dns-spoofing']: dns_spoofing_flag = True if arg in ['-p', '--printer-sim']: printer_sim_flag = True if microsegment_flag: setup_microsegmentation() if start_captive_portal_flag: os.system('iptables -I FORWARD -j NFQUEUE --queue-num 0') queue = netfilterqueue.NetfilterQueue() queue.bind(0, redirect_traffic) start_captive_portal() def signal_handler(signal, frame): os.system('iptables --flush') queue.unbind() sys.exit(0) signal.signal(signal.SIGINT, signal_handler)
http://queue.run
() if log_flag: setup_logging() if dns_spoofing_flag: dns_spoofing_thread = threading.Thread(target=dns_spoofing) dns_spoofing_thread.start() if printer_sim_flag: wireless_printer_thread = threading.Thread(target=simulate_wireless_printer) wireless_printer_thread.start() else: print("Usage: python advanced_network_control.py [options]") except Exception as e: log_event("ERROR", str(e)) if __name__ == "__main__": main()
Little did I know that I fell for Sebastian’s manipulative lies and later on noticed that the account’s all tied to GhostSec420 lead to the identity of Michael Errington (His real name) and not Sebastian Dante Alexander and that there actually is no fake GhostSec in Telegram and that all of it leads to the identity of Michael Errington himself. As we are going to uncover the mystery behind Mr. Errington below, we shall see the truth of who exactly he is:
Tracing down Michael Errington.
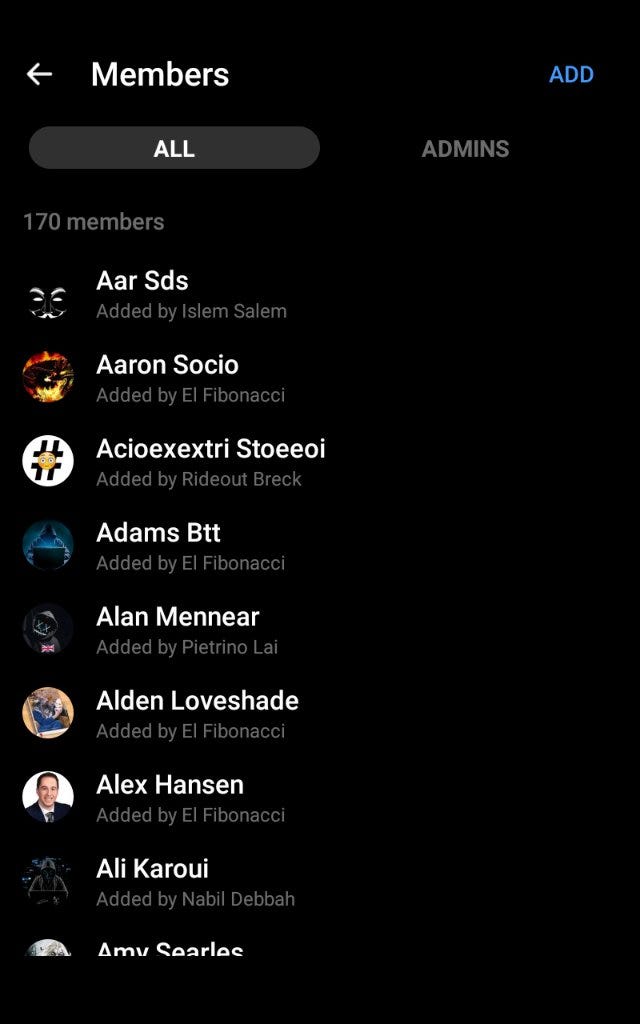
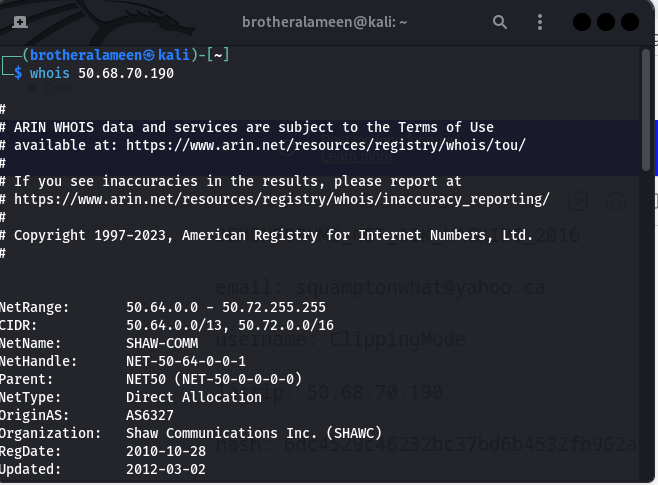
The tracing of the identity of Michael Errington wasn’t a hard job, especially since I had someone with the right tools to do it. In this manner, we used Slosint for the email since we couldn’t get an intelx subscription, but it still revealed a lot about Mr. Errington whose email is supposedly tied to the GhostSec Account on Instagram, including his IP Address tracing to Shaw Communications in Canada.
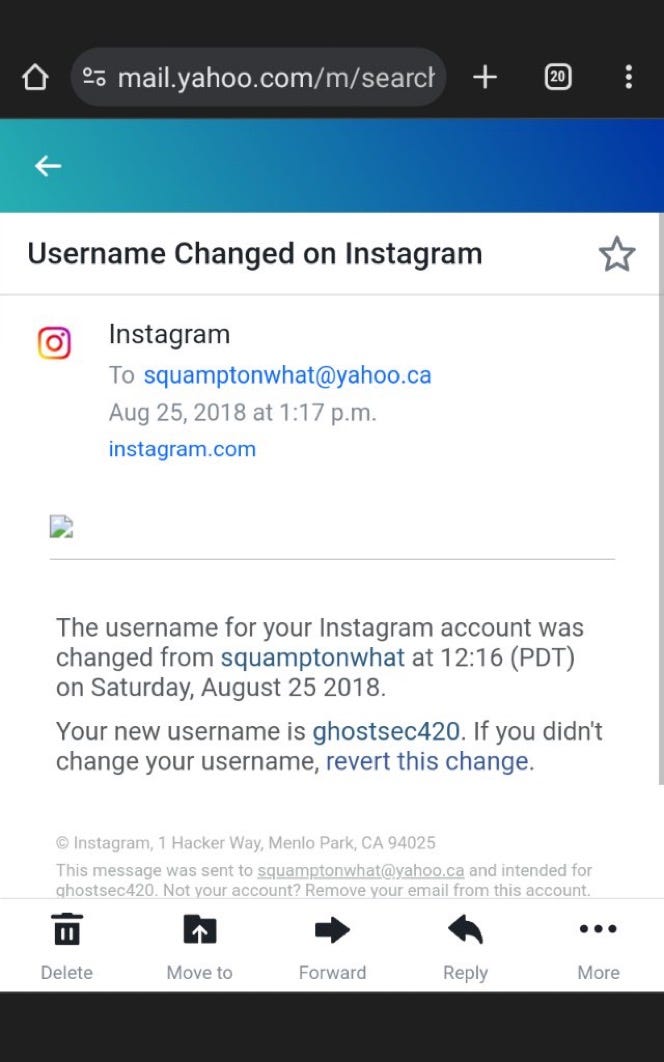
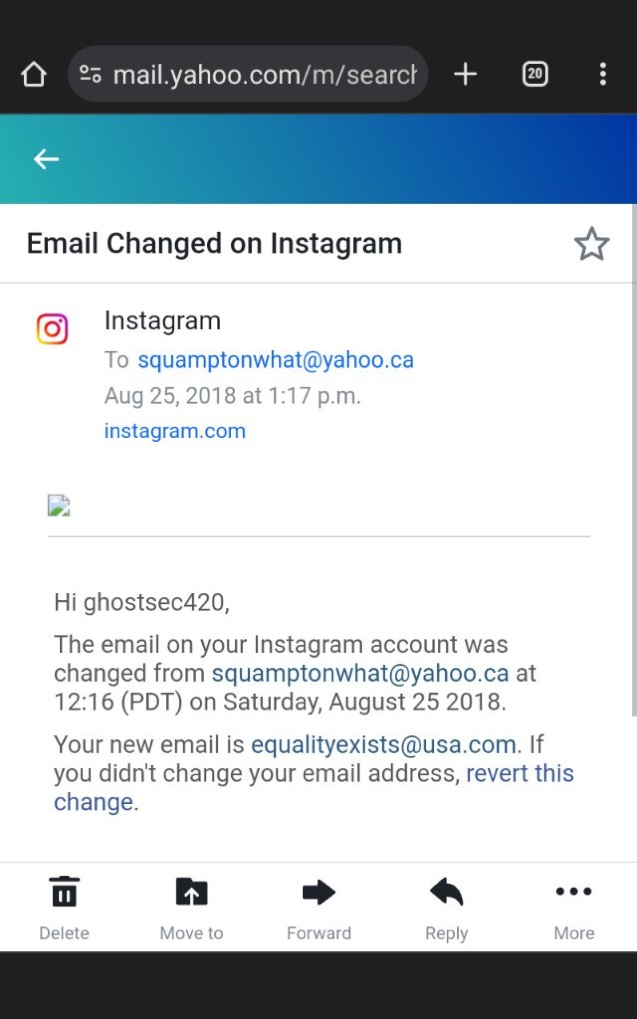
It all began when he began to bring out more information about Akram, including his email changes and username changes in Instagram, as we shall see below:
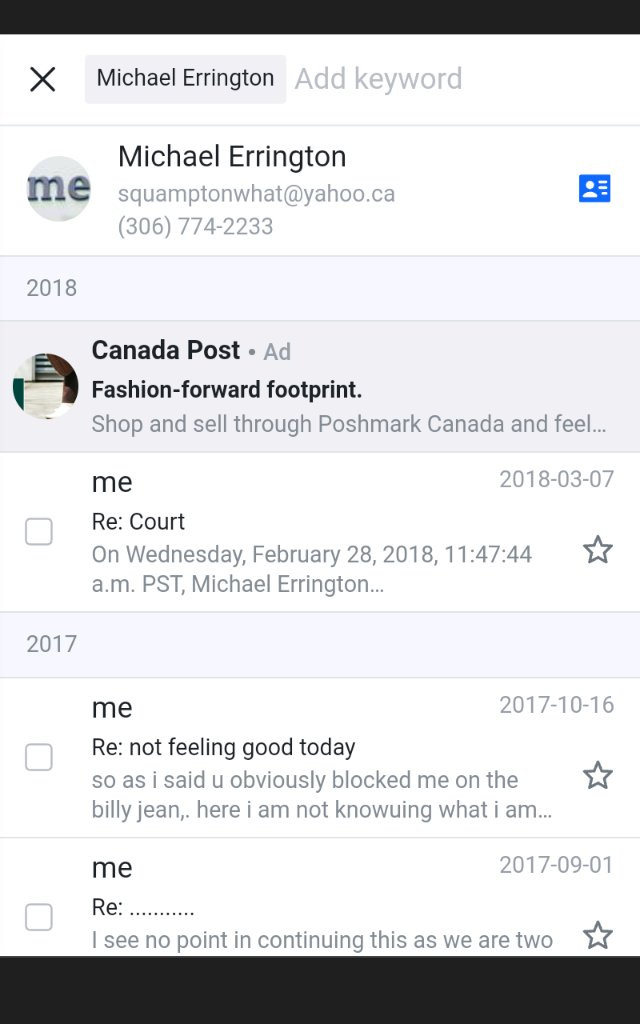
As we can see here, the username changed from squamptonwhat to ghostsec420 on Instagram, and if we see below, he changes the email of the Instagram Account from squamptonwhat@yahoo.ca to equalityexists@usa.com, which I believe is tied to him as well:
As you can see, the way the email is structured made it seem like as if the way he was explaining about GhostSec being two different people is true but that isn’t the case, as we shall see below, the data retrieved back from slosint proved otherwise:
INSTANTCHECKMATE_COM_11M_PRIVACY_042019
email: squamptonwhat@yahoo.ca
hash: c2NyeXB0AA4AAAAIAAAAAbm61dUOBRSywLe9RF7U5RTKjJW8MoPHdFviL0N/NLYKEPrHwHgBfVaidabz3xA76pXvYLqQXg4HmVdmT9oDM97VVRlTeygSWQ7YTq1jng2R
name: mike errington
PS3HAX_NET_447K_HACKING_072015
email: squamptonwhat@yahoo.ca
username: Squamptonwhat
lastip: 50.68.81.106
hash: 22276f761c9c0401000371f1e7fef3a3
salt: LE5cx>Xe?Byq`zQmc%qPL*XKR2$inX
ARMORGAMES_COM_11M_GAMING_012019
email: squamptonwhat@yahoo.ca
username: squamptonwhat
lastip: 50.68.74.158
hash: 741be38857315b8808bd26b1b52aba4b24bfcbb9
ADULTFRIENDFINDER_COM_220M_DATING_2016
email: squamptonwhat@yahoo.ca
username: KingShlong1981
hash: 2c59e91efd712af71597a6b1d11904f4bc13880d
DEMONFORUMS_NET_52K_HACKING_022019
email: squamptonwhat@yahoo.ca
username: ClippingMode
lastip: 50.68.70.190
hash: 6dc4529c46232bc37bd6b4532fb962a0
salt: o34OpFUR
PEMIBLANC_COM_134M_COMBOLIST_2018
email: squamptonwhat@yahoo.ca
password: zaq11qaz
2844_DATABASES_218M_COMPILATION_2018
email: squamptonwhat@yahoo.ca
password: zaq11qaz
DEMONFORUMS_NET_11K_HACKING_2016
email: squamptonwhat@yahoo.ca
username: ClippingMode
lastip: 50.68.70.190
hash: 6dc4529c46232bc37bd6b4532fb962a0
salt: o34OpFUR
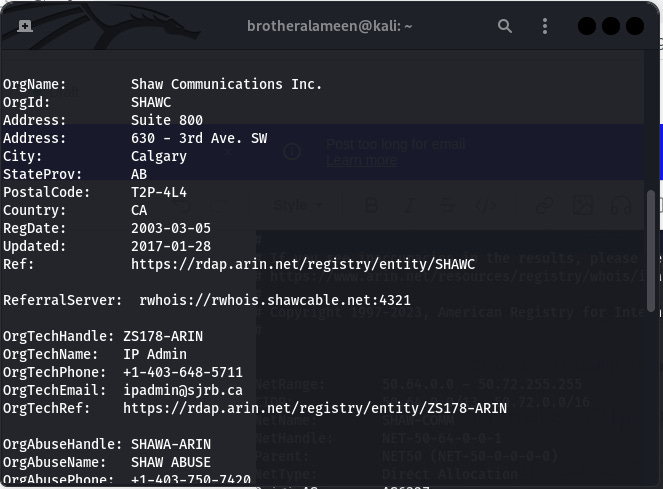
As seen above, the slosint data reveals an IP Address, which if we run a whois on, we get Shaw Communications, Canada, not to forget that the email itself is Canadian as well:
This simply means he’s not been using a VPN and his communication isn’t encrypted. Inclusive to this, slosint even reveals a familiar name: Mike Errington, as seen on the retrieved data that we have from slosint for Instant Checkmate.
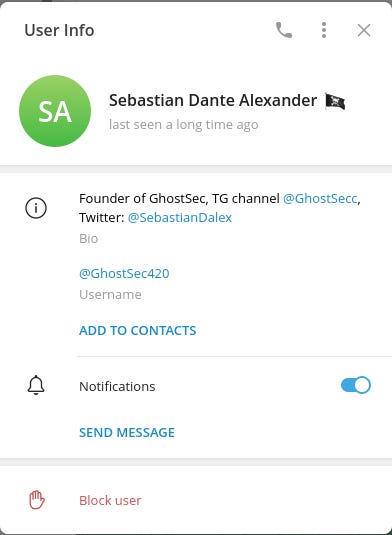
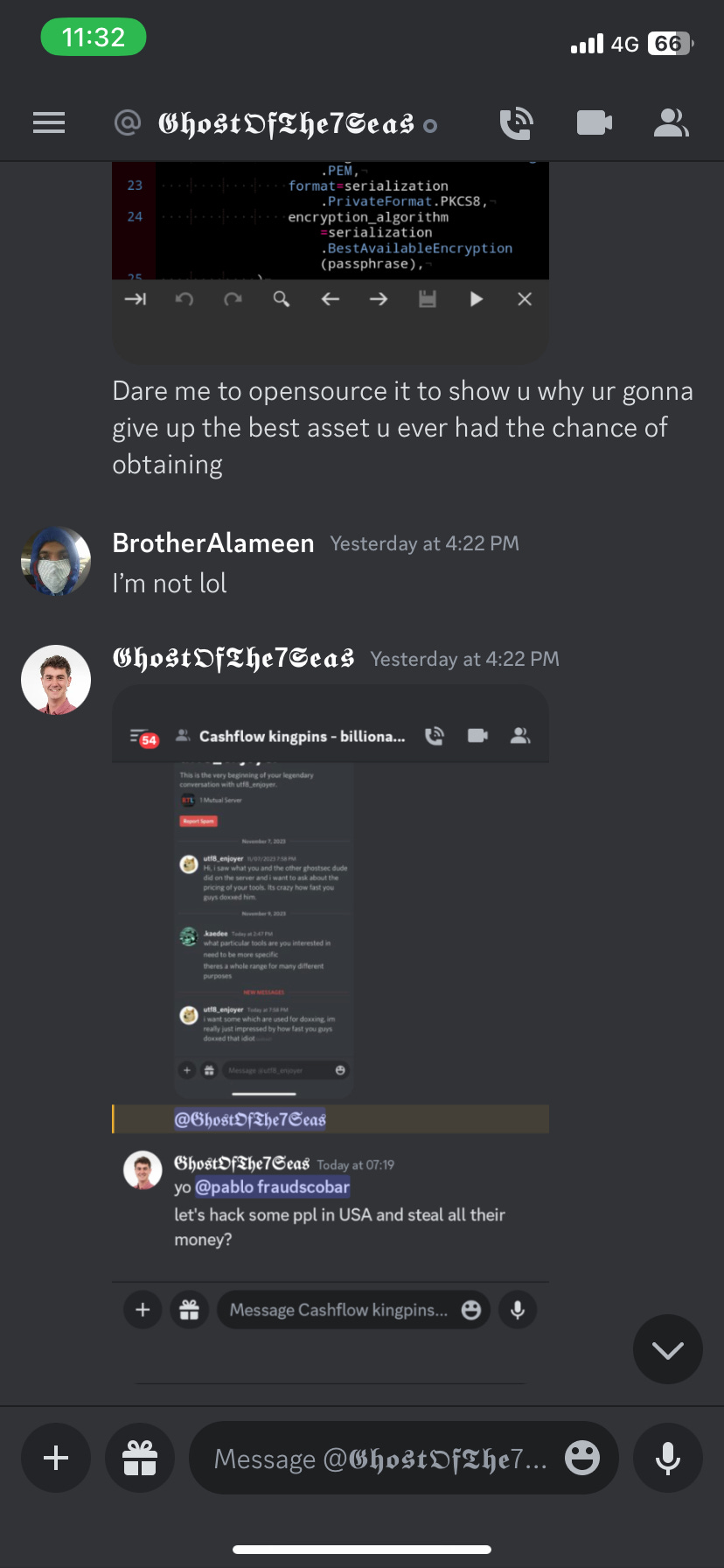
We can further tie this information to the Sebastian on Telegram and Twitter using using the usernames Equality Exists and GhostSec420, as seen below:
As we can see that the Telegram Account has ties to the Instagram Username GhostSec420 which was tied to squamptonwhat@yahoo.ca that the slosint data revealed is tied to Michael Errington.
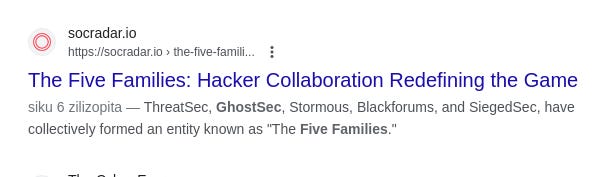
Over here, we see the connection again through his Twitter Account and we see he’s followed by members of the Five Families including SiegedSec, this is simply because GhostSec is part of the Five Families. To tie the two Twitter Accounts together to show they’re from the same person, we must understand that the only person with tools that are built for GhostSec and claims that he is giving the necessary requirements to GhostSec is Michael Errington himself, and to tie this further, we even see that Michael Errington and Sebastian Dante Alexander share the same profile picture as well:
As we can see that the photos of both these accounts are the same, to further illustrate by means of connection, look below:
Now, we have to further tie these accounts to the Sebastian in Telegram, to understand better, we see that Sebastian is the owner of GhostSec. Nonetheless, his real name is Michael Errington from Canada and to understand that this is his real life name, we need to further look at the information that ties the name Michael Errington to his Phone Number:
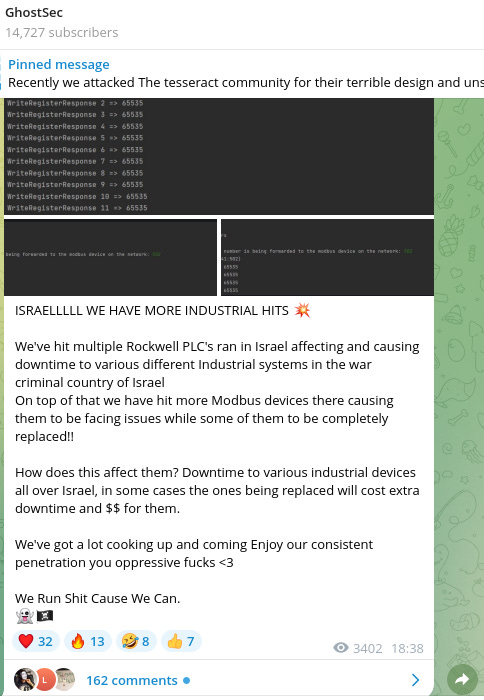
As we can see above, that the identity of a Michael Errington does in fact tie itself to his real name and the location being in Canada. To further prove that he is behind the tools that are used by GhostSec on Telegram, we must check the recent attacks that GhostSec has had over Israel, this can be observed from the Telegram Channel that’s tied to his Twitter Account and his Telegram Account:
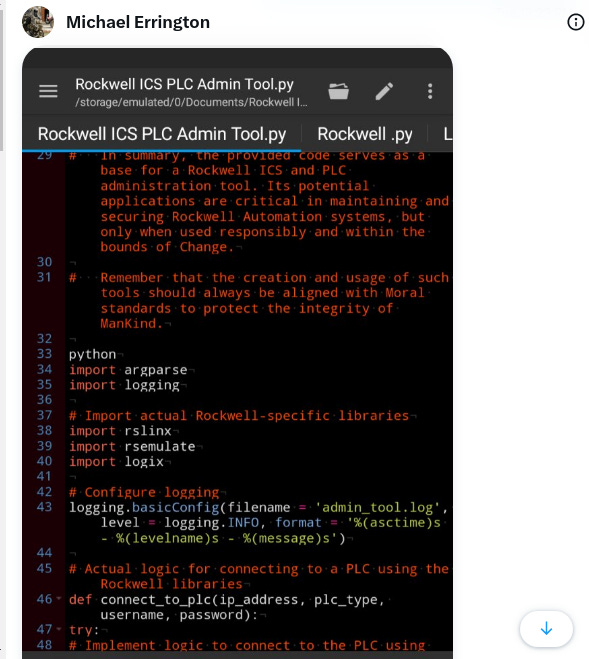
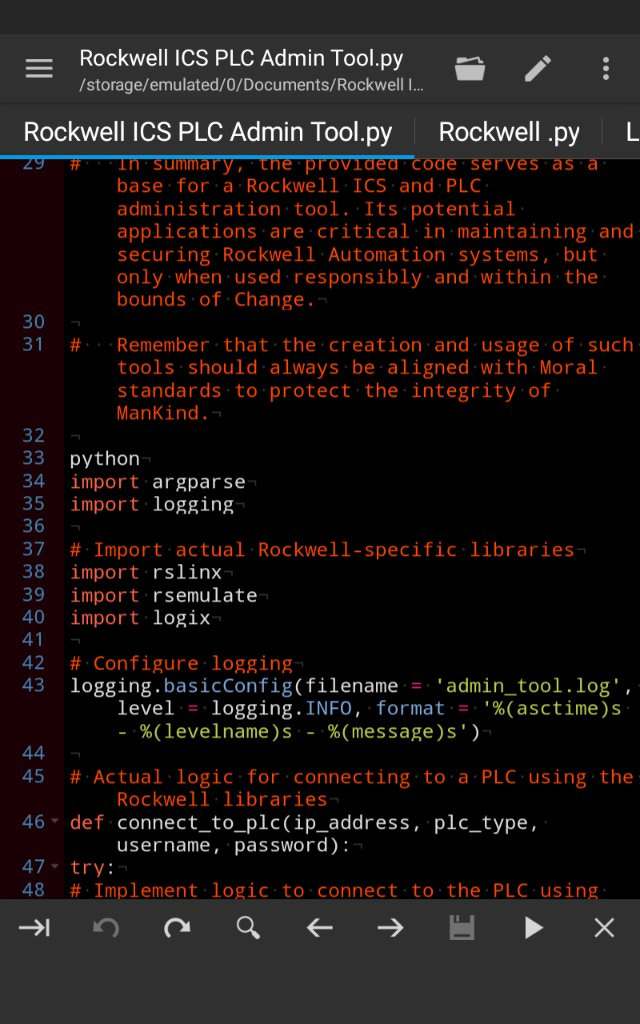
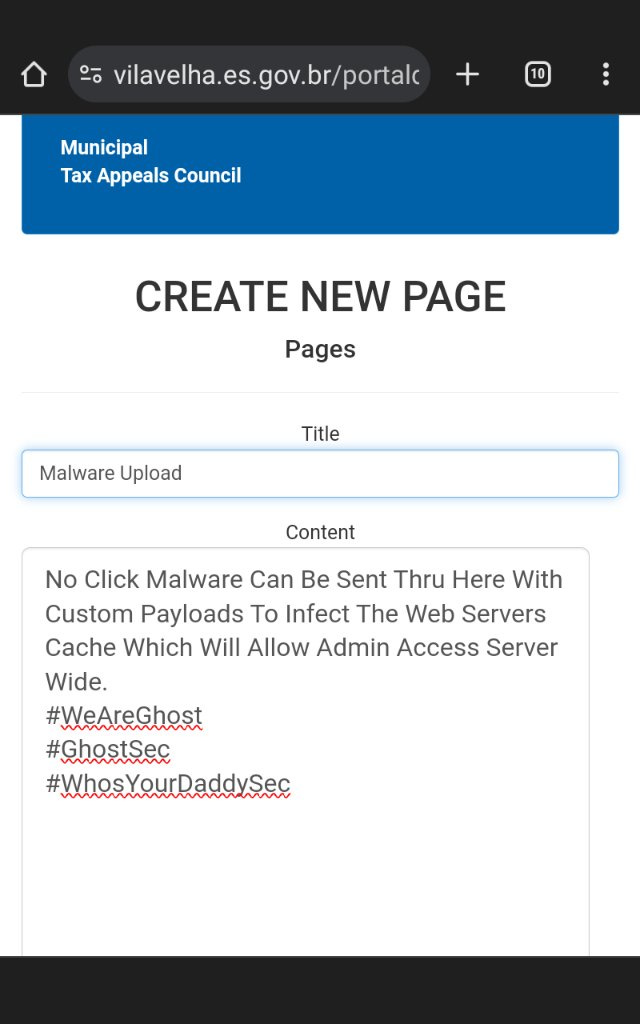
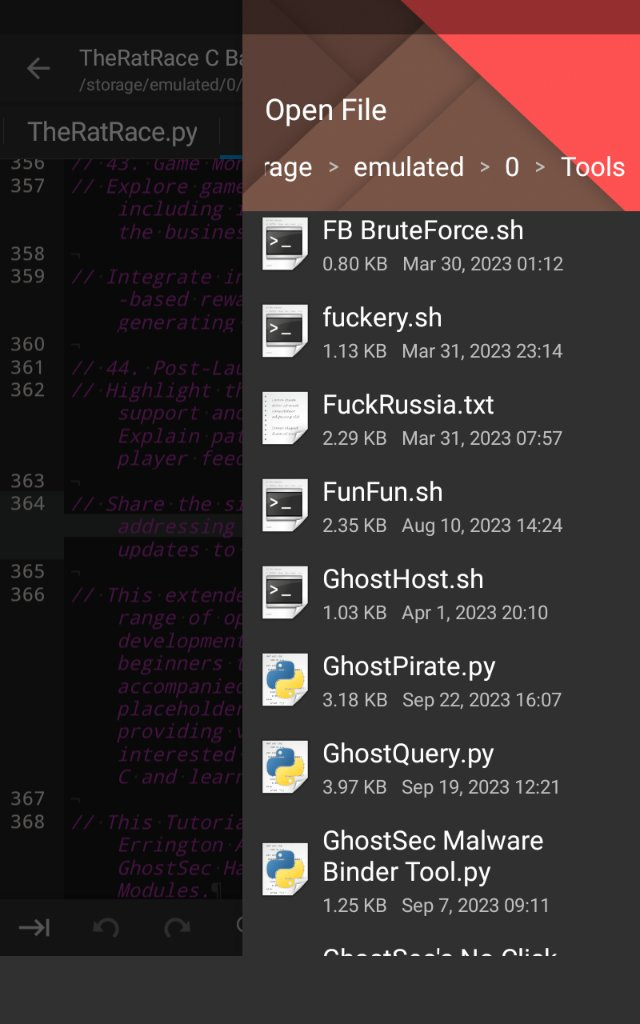
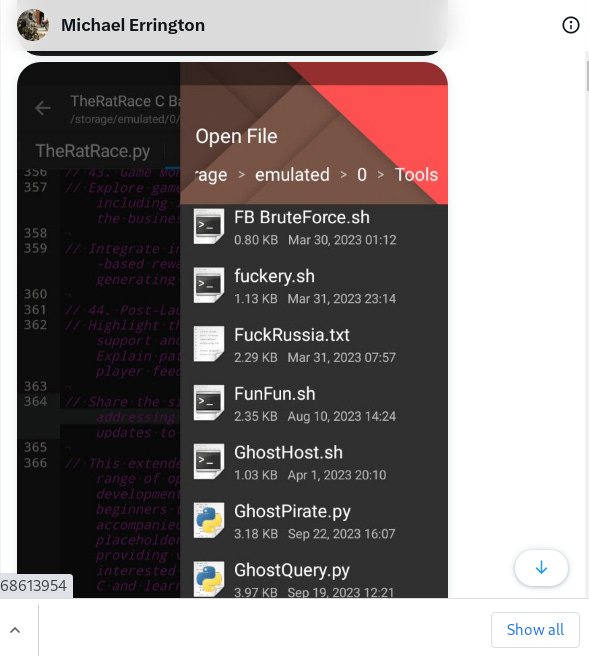
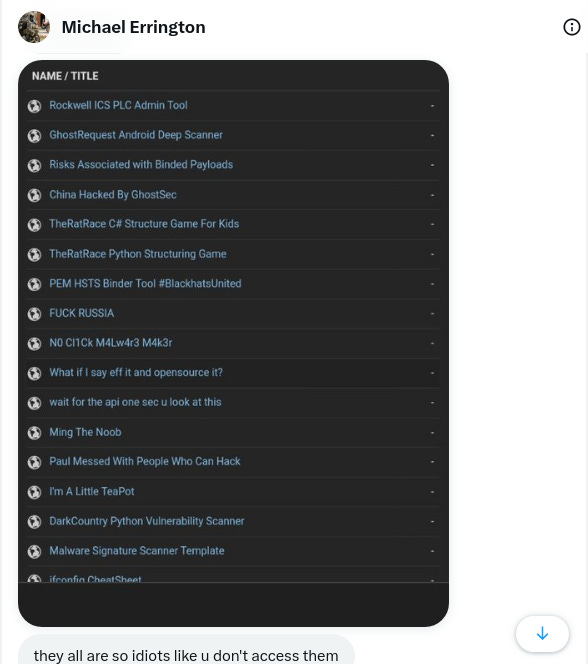
Over here, we see that GhostSec hit Rockwell PLC in Israel, but if we look into Michael Errington’s chat, we see he is the person with the tools to hit Rockwell PLC:
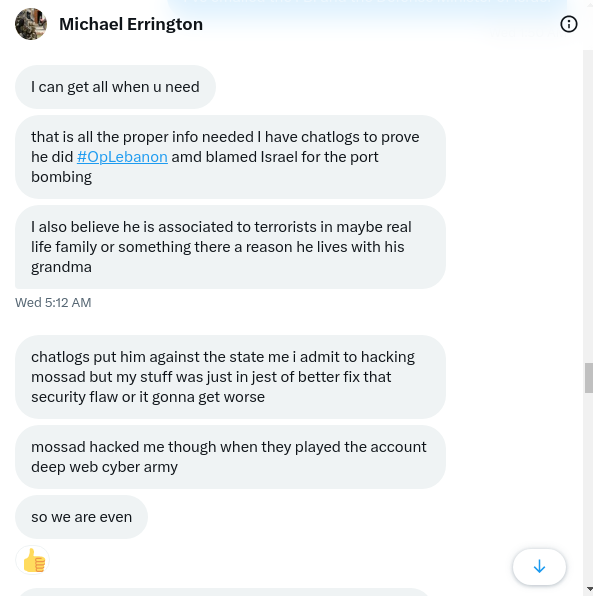
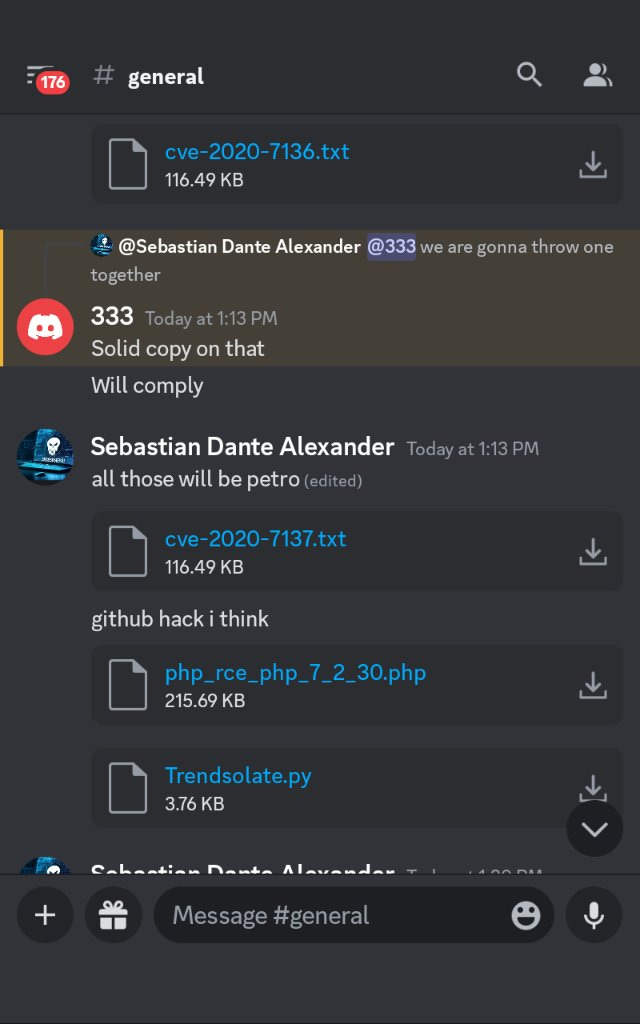
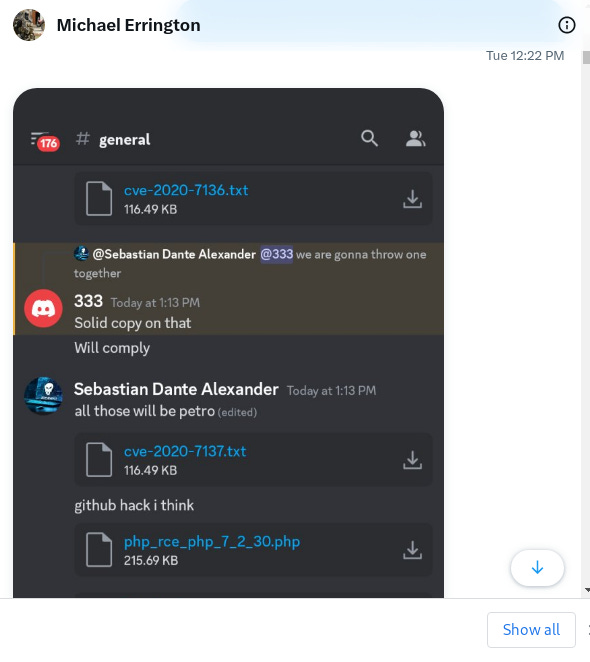
We even further see from the chat that he is the person with all the tools that are used by GhostSec as well and that he his the one hitting Governments with zero-day attacks that have been identified and made by himself:
As we can see and conclude from all these screenshots above, that all of this ties to Michael Errington, at the end of the day. The tools used by GhostSec, the emails, the username changes and everything on GhostSec. To further tie GhostSec to the five families, we can take this article from a reputable cyber-security source named SOCRadar.
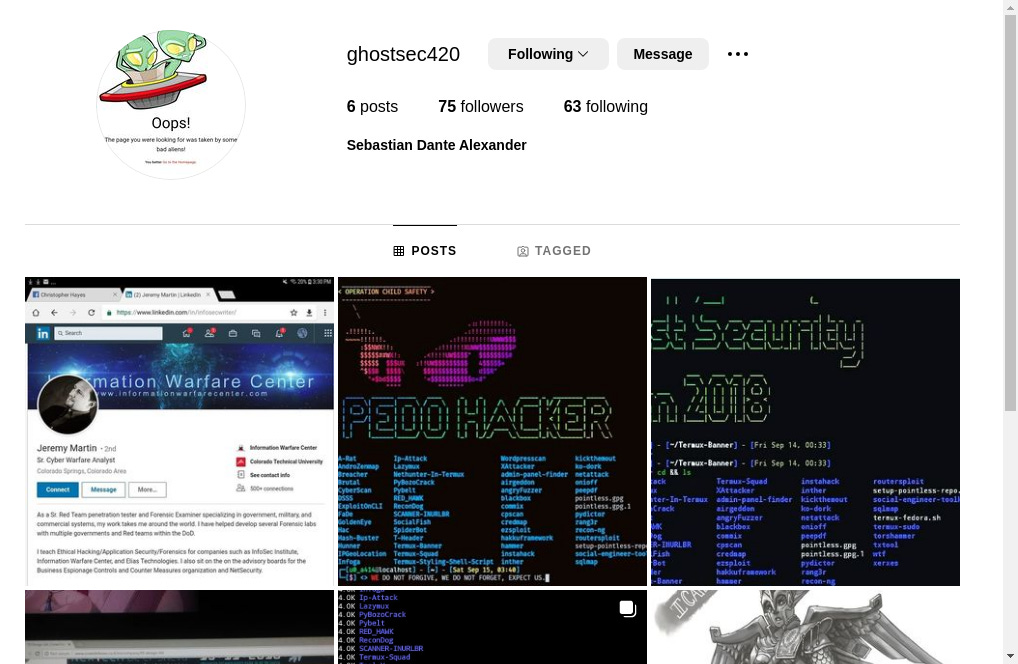
We now get to see the full picture that Michael Errington is actually Sebastian Dante Alexander himself, all of this leading to him being behind everything isn’t a coincidence at all and it’s all making perfect sense from the OSINT. Also, if we look at the Instagram Account:
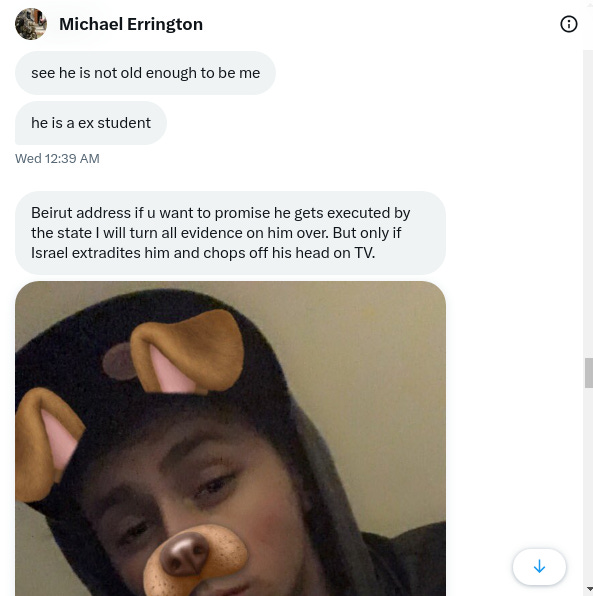
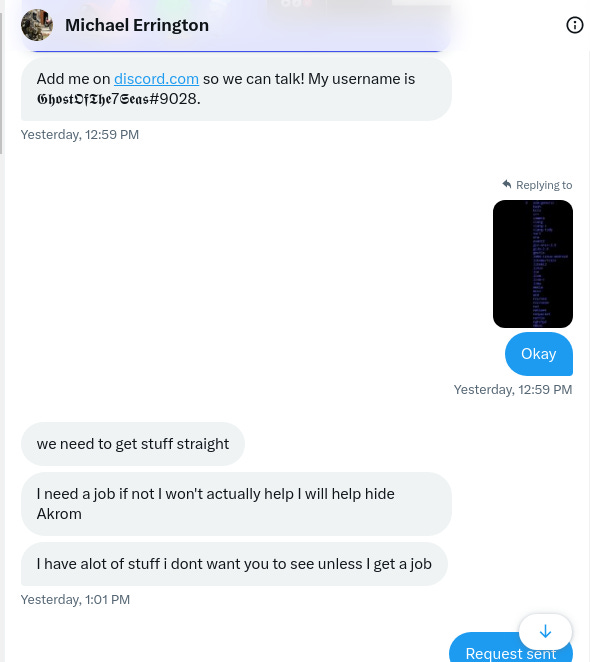
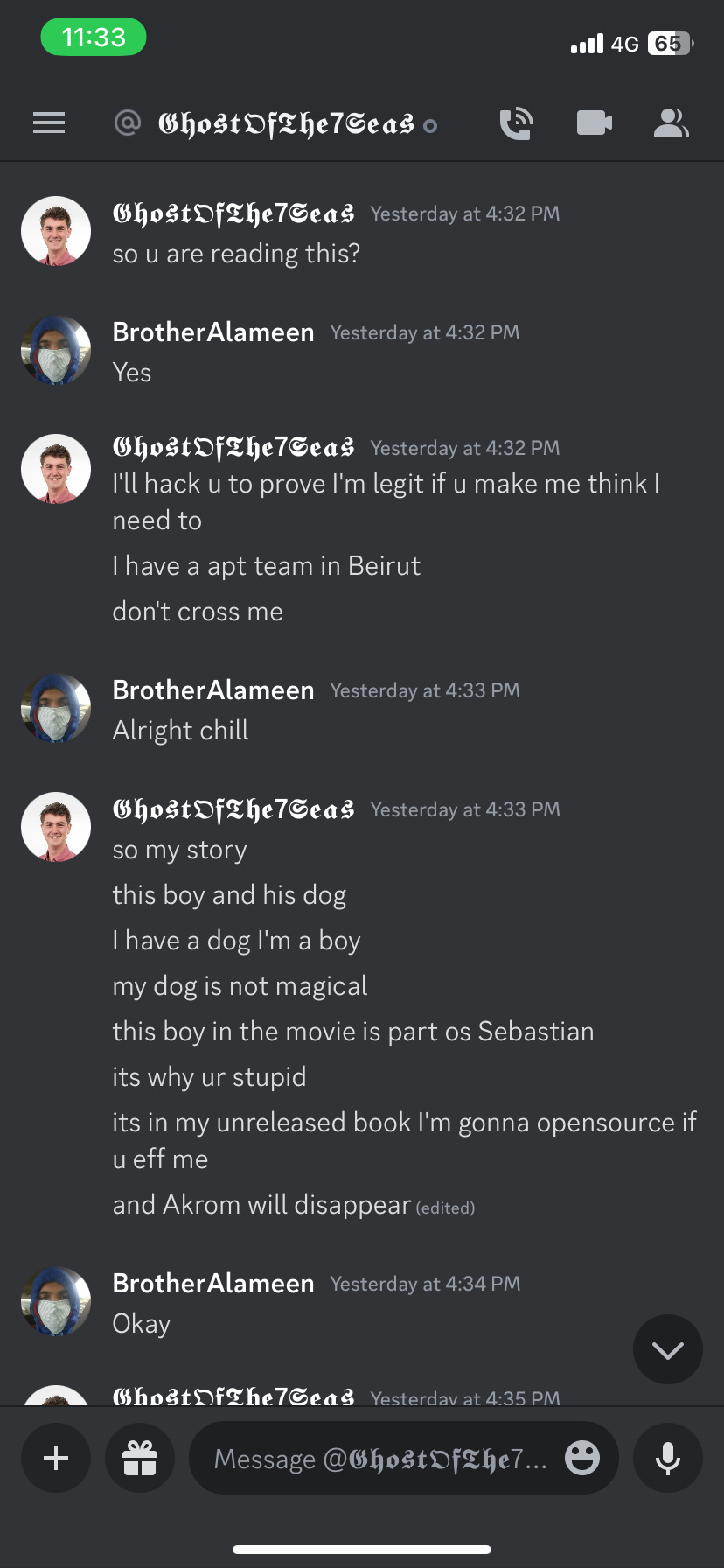
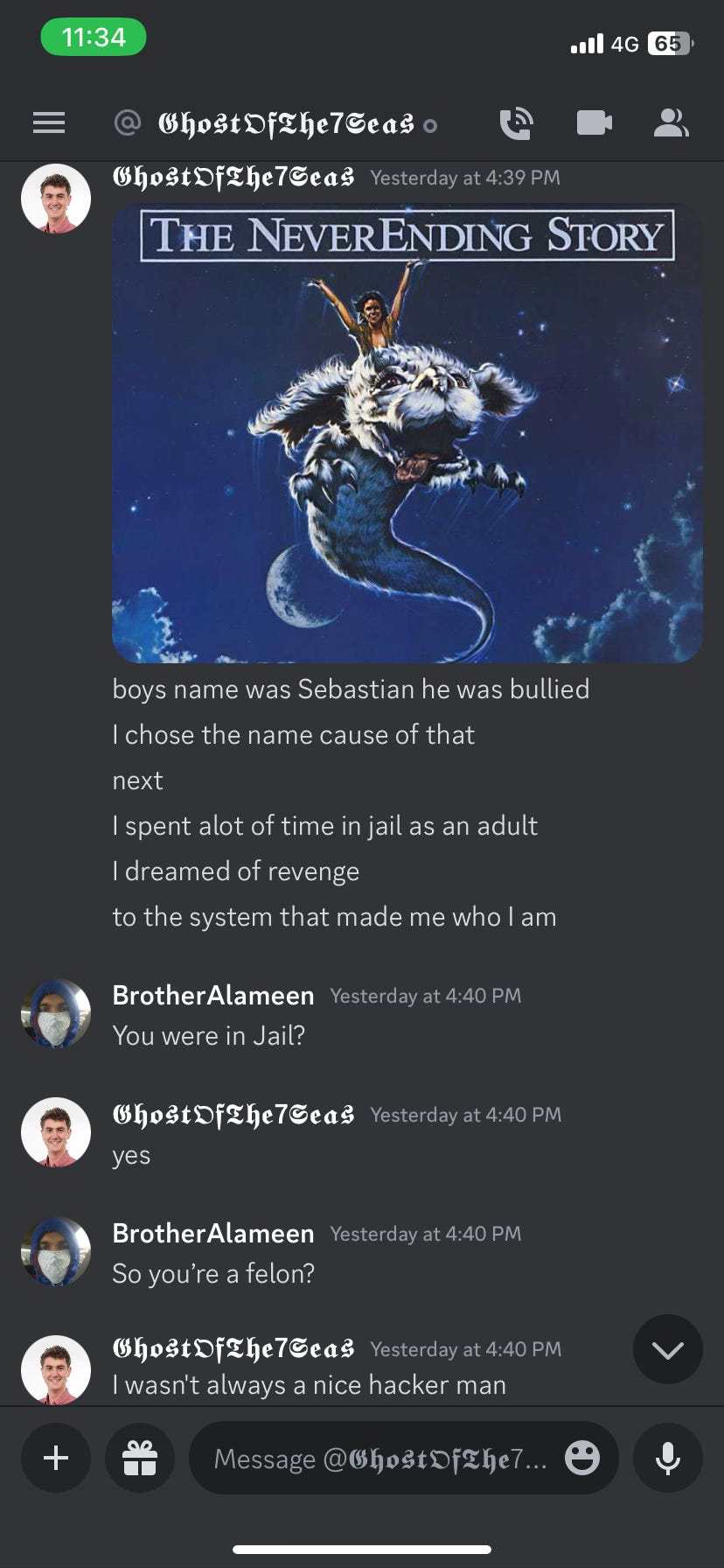
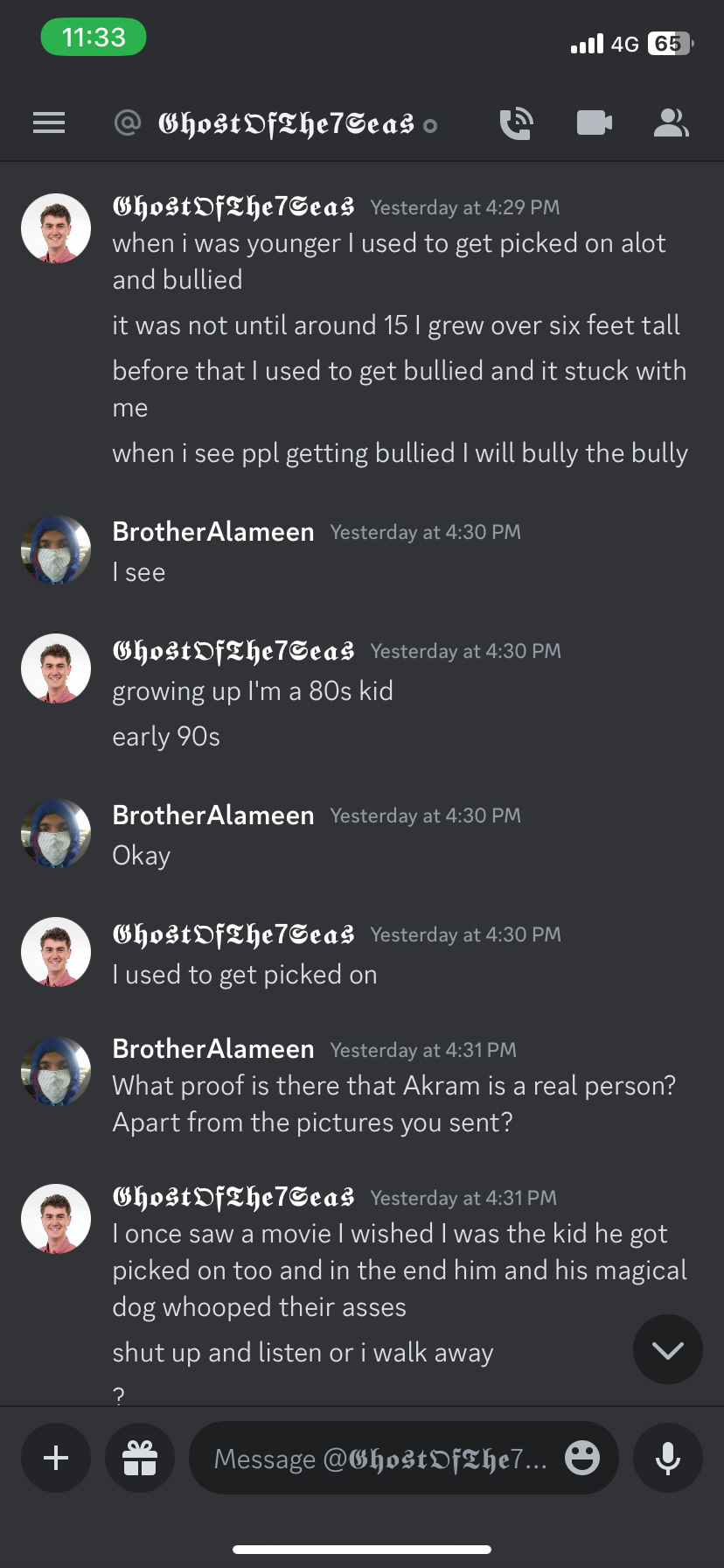
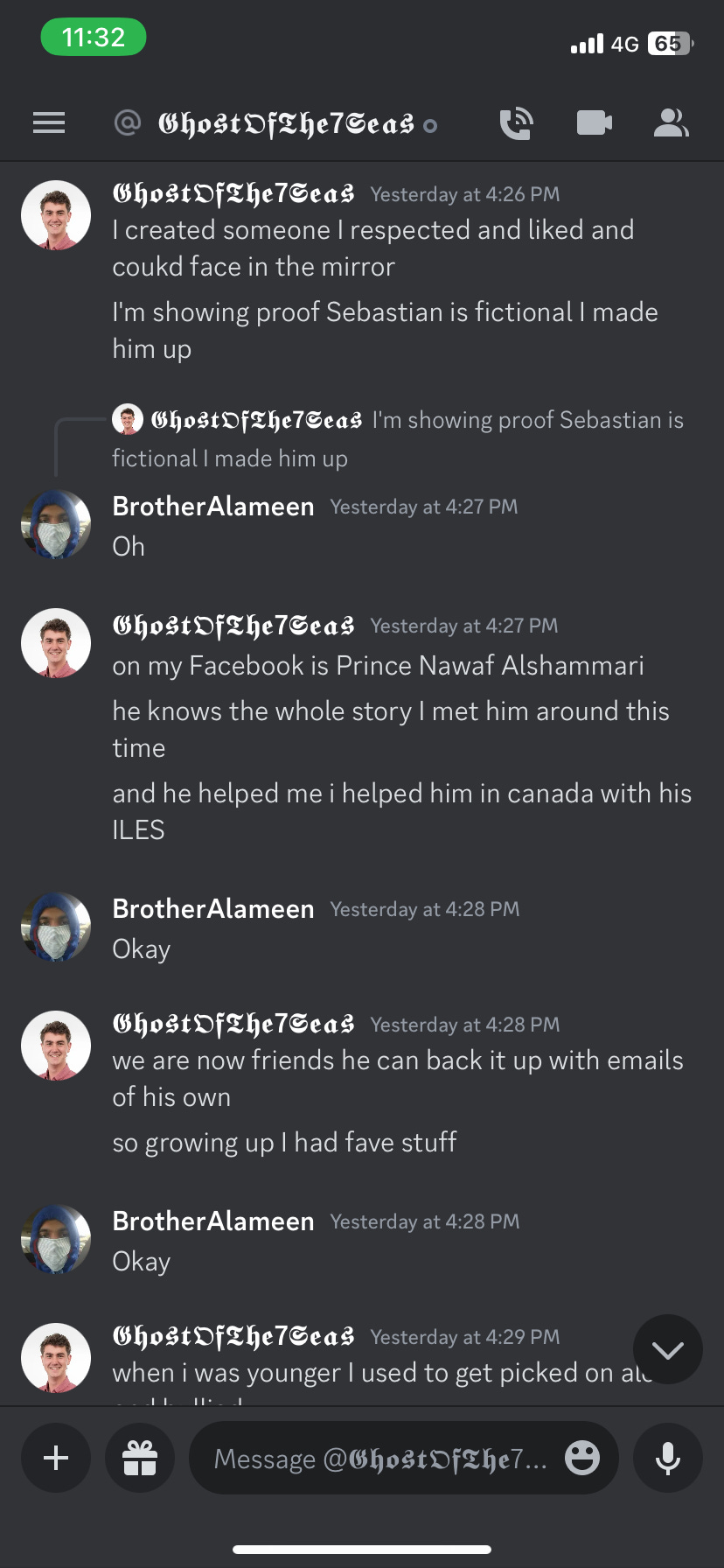
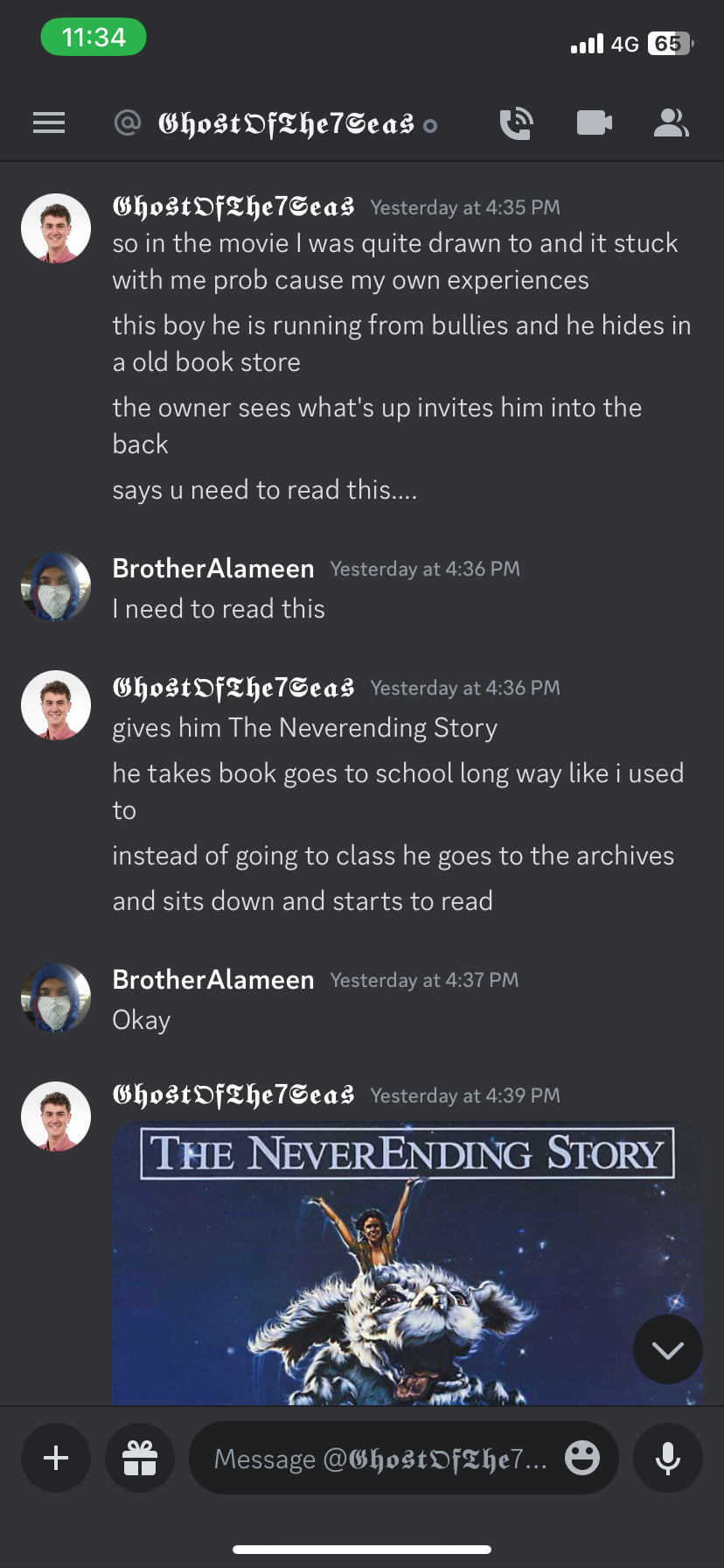
We can see that it’s tied to Sebastian Dante Alexander. He also asked that I should add him to Discord as well, while in the Discord chat, he revealed a lot about himself, even went on to say that he was in Solitary Confinement for three years because he wasn’t that much of a professional hacker, then eventually finished by confessing his name as Michael Errington and said that the name Sebastian Dante Alexander and Akram came into existence through a novel that he read since he was a kid which contained the character Sebastian Dante Alexander and Akram himself, proving therefore that Sebastian Dante Alexander and Akram are fictitious characters from a novel and that the identity ties to him being Michael Errington himself, all of which happened after I showed him the information from the slosint scan:
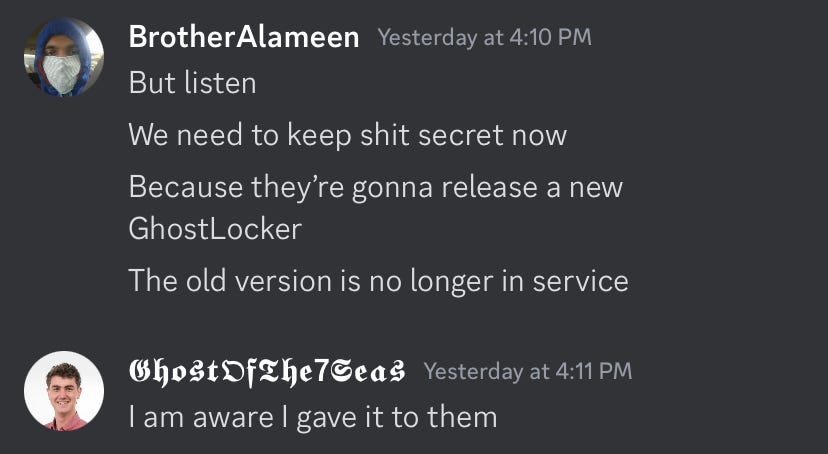
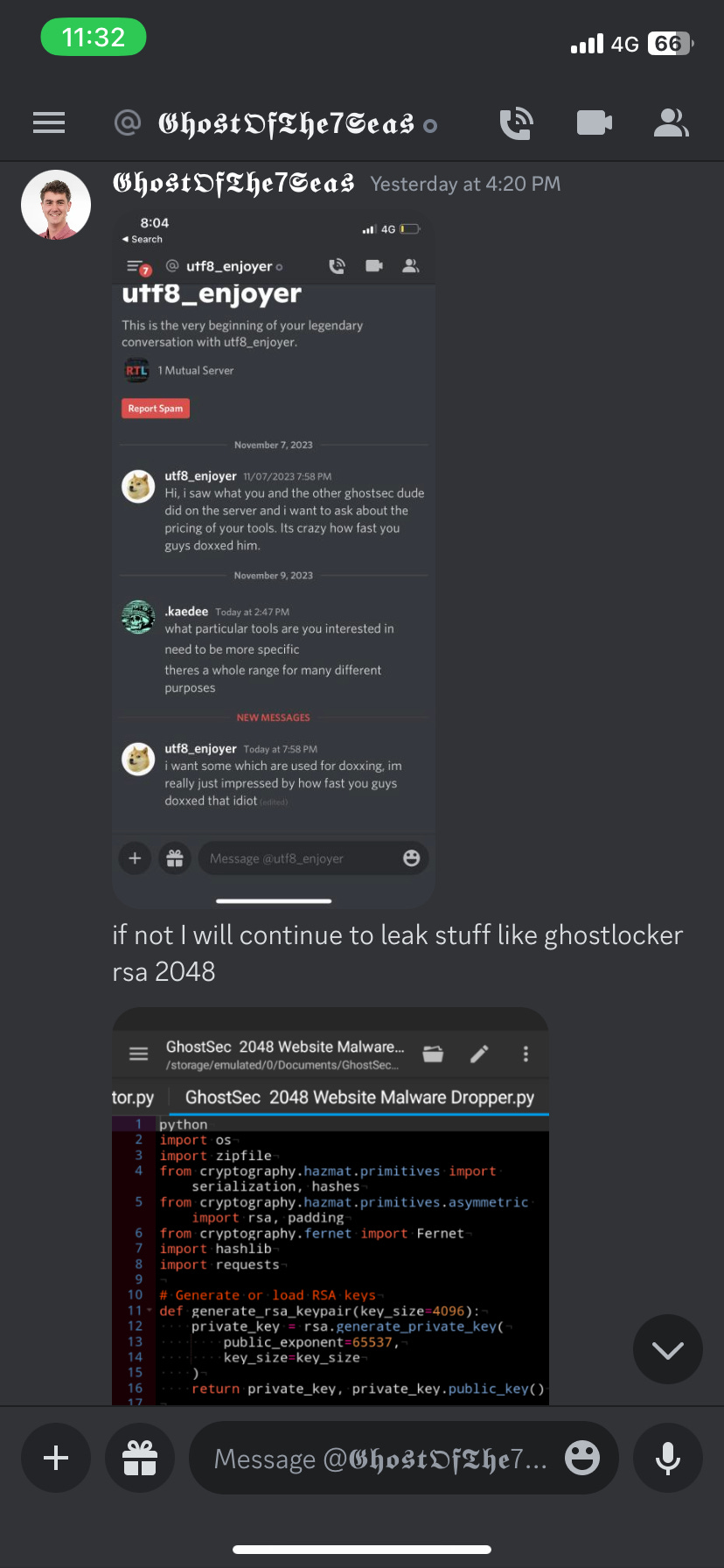
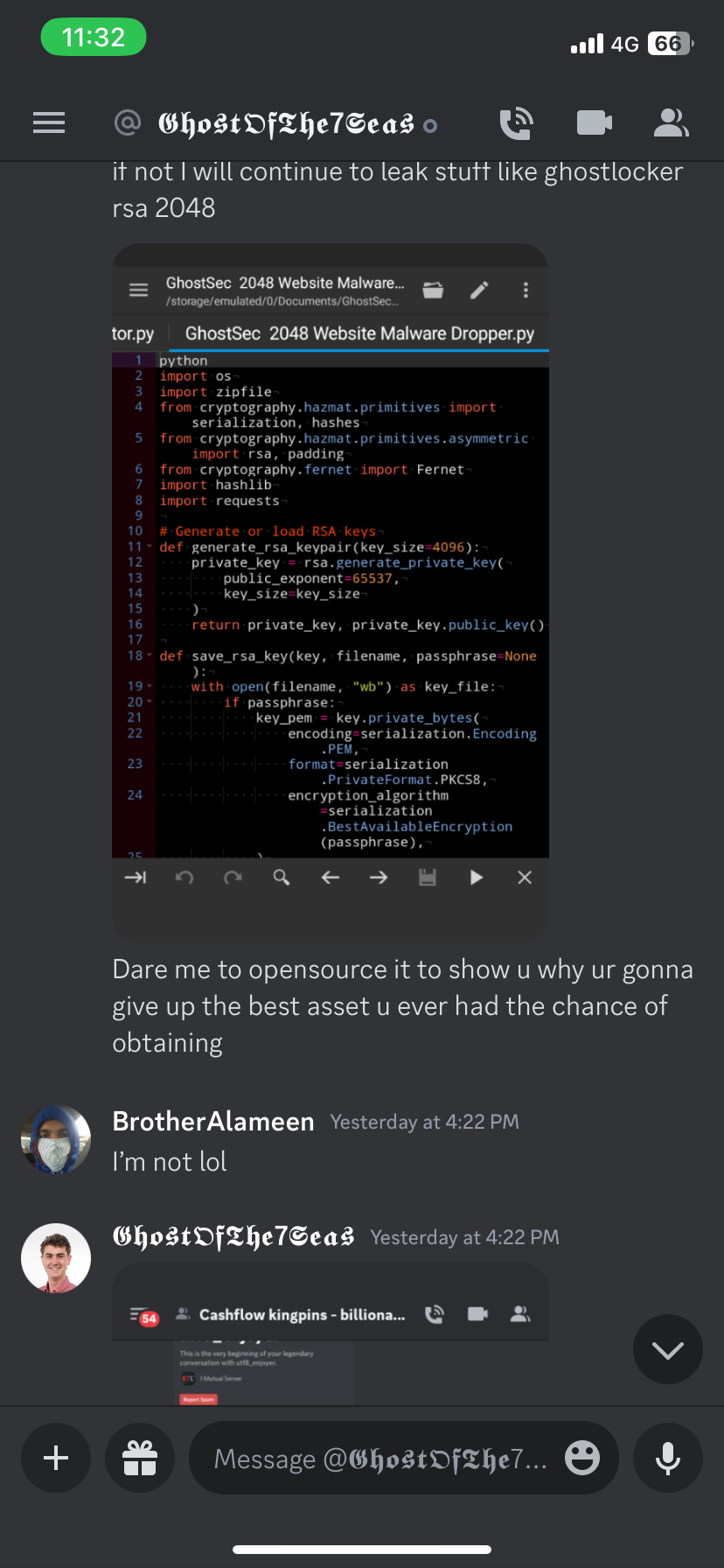
Over the chat Discord (𝕲𝖍𝖔𝖘𝖙𝕺𝖋𝕿𝖍𝖊7𝕾𝖊𝖆𝖘#9028) chat, he even reveals that he is revamping the entire source code of the GhostLocker Ransomware, and showed the sample of the new source code of the ransomware as well, which further proves that this Sebastian Dante Alexander himself, he even further says he has an APT Team in Beirut, which is literally the Capital City of Lebanon:
So, as we can see from the above screenshot, this all ties to Michael Errington creating Sebastian as a fictitious character, and him further saying that he’s behind the GhostLocker Ransomware. To tie this to the GhostSec Telegram Channel, we are gonna use this screenshot from their channel which talks about the GhostLocker:
This once again is from the same channel tied to Sebastian’s Telegram Account and Twitter Account as shown previously (@GhostSecc). We can further see that he is in possession of Sebastian’s Discord as well:
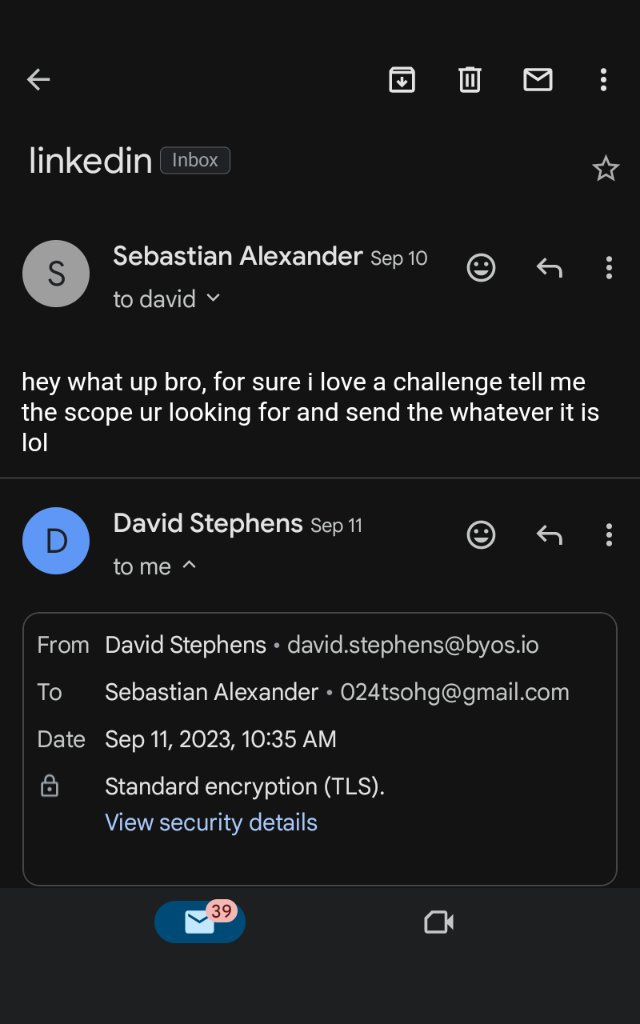
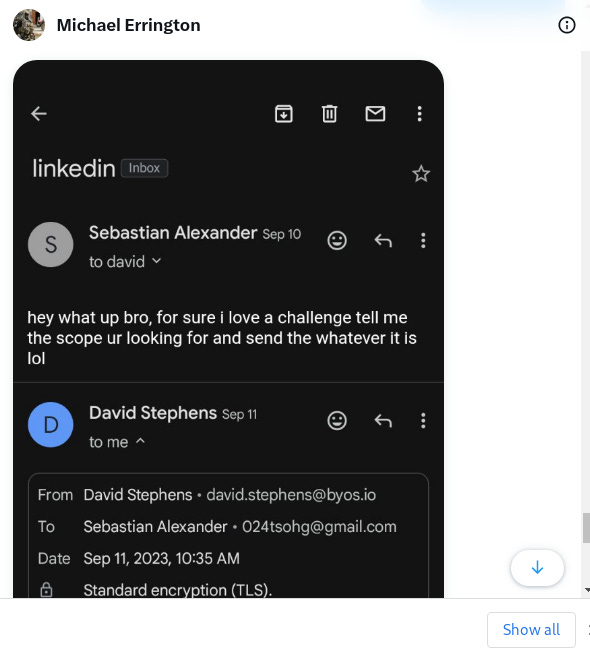
And he’s in control of Sebastian’s email as well, as seen in the screenshot below:
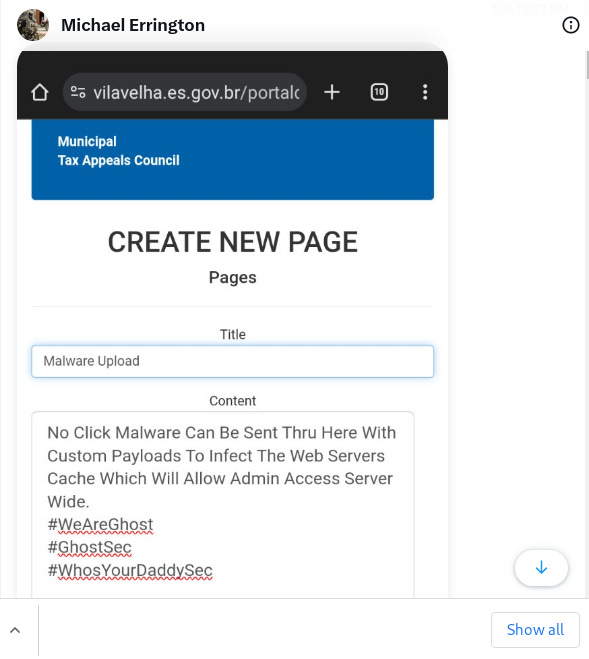
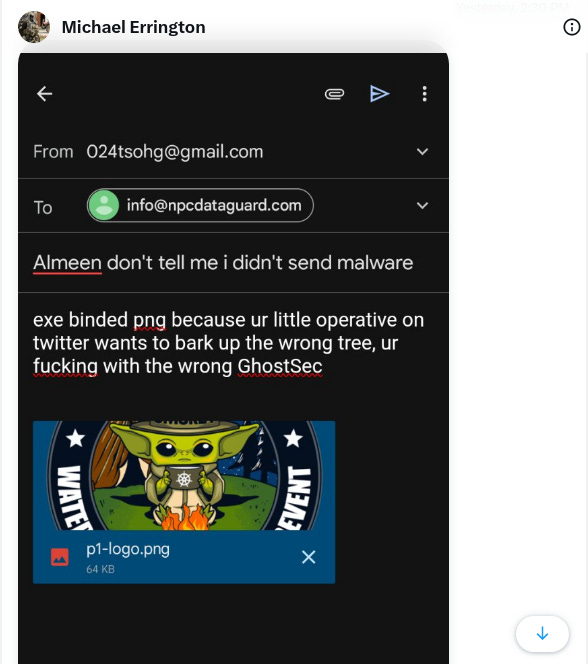
As we can see that the email ties to Sebastian Alexander, 024tsohg@gmail.com. Over here, we shall see himself sending malware using his zero-day attack to the NPC Data Guard using the Sebastian Email:
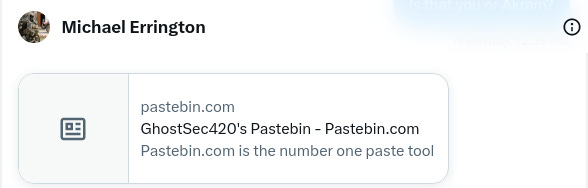
Him thinking that my CEO in Twitter is messing with him. Of course, I don’t use Twitter and haven’t used it in long, it’s my CEO that does and whom was communicating with him, since I’m the CFO. We can further see that he has a pastebin below, which ties to GhostSec420 as the username, this further reveals that he uses PasteBin to upload his tools source code and dox people as well:
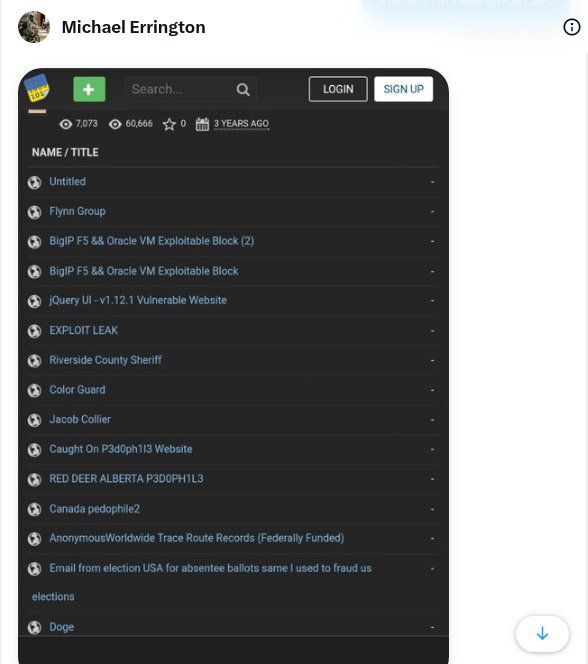
Now with the screenshot below which he revealed, we see that the username of the Pastebin Account he handles is in fact, GhostSec420. This ties to both the Instagram Account and the Telegram Account as well:
While it’s true that he doesn’t have any Public Pastes, using his information from slosint and a little bit of Social Engineering, he revealed the screenshots above, showing what pastes he’s made private.
Conclusion:
While many may think that an Akram exists through Sebastian’s manipulative techniques, he doesn’t. The photos, I’m pretty sure ties to himself, Michael Errington and not the non-existent GrimSec that he’s talking about. Nonetheless, this comprehensive document showing all information that ties GhostSec to Michael Errington leads to the proof that he indeed is Sebastian Dante Alexander himself. The whole Akram thing was his method of hiding his identity so he wouldn’t be known while exposing himself, which is kind of pretty dumb for the fact that he exposed all the tools and information tied to his email and his phone. There isn’t any coincidences to tie GhostSec as Michael Errington being the owner of it with all the proof above that ties the accounts to him, including the privated pastes.